Art of Making Real-Word Ransomware in Java and Defense!
Protect yourself and your network against Ransomware Attacks by Making your own Ransomware

What you will learn
Understanding differences between various categories of malware in real-world hacking such as ransomware, trojan, and keylogger in ethical hacking
Learning cryptography basics in a simple language for ransomware design
Learning essential Java basics for writing a real ransomware in Java
Creating a basic cross-platform Ransomware Program that works on Windows, Linux, and macOS.
How to detect victim host operating system and finding worthwhile files for the encryption
How to detect a ransomware in your system
How to perform reverse engineering on a ransomware file
How to find keys without contacting the attackers
How to recover your encrypted files with reverse engineering on the ransomware file
Why take this course?
* Course Description
In this course, you will learn how to create real-world Ransomware from scratch in Java. By watching each video of this course and following the practices, at the end of this course you have your own cross-platform (running on Windows, Linux, and Mac OS) Ransomware, which helps you to a real Ransomware attack, and how should you protect yourself, your network, and your company against various Ransomware attacks.
This course's primary motivation is to share the necessary knowledge and experience about Ransomware design by an experienced malware analyst. Moreover, in this course, you will receive the basic understanding of Java programming necessary for ransomware design and the basics of cryptography in Java. Finally, this course provides multiple exercises, articles, and source codes to help you out to follow the course milestones.
* Special Certificate
After finishing the course you will receive a certificate. However, there is an option for the super certificate in which you need to implement the final project and send it to info@hackerburg.io. As a result, you will receive a special certificate in addition to the Udemy certificate. This certificate will be issued by a team of Cybersecurity experts by evaluating your solution.
* Who is it for?
Beginners, programmers, and cybersecurity specialists, developers, QA experts, system administrators, and novice bug hunters.
* Benefits of Buying this course
Unlimited access to all contents including solutions
Unlimited access to the non-public papers, source codes, and extra exercises
Having direct chat with the teacher for getting technical advice, solving exercises, and sharing technical issues
* Bonus:
Those folks who buy this course will be able to access the videos, articles, and source codes. Moreover, the buyers chat with the teacher directly and ask their technical questions unlimitedly.
* Attention:
This course is provided for educational purposes only, so HackerBurg and the teacher do not take any responsibility for the misuse of the content, resources, and knowledge provided by the course!
Screenshots


Reviews
Charts
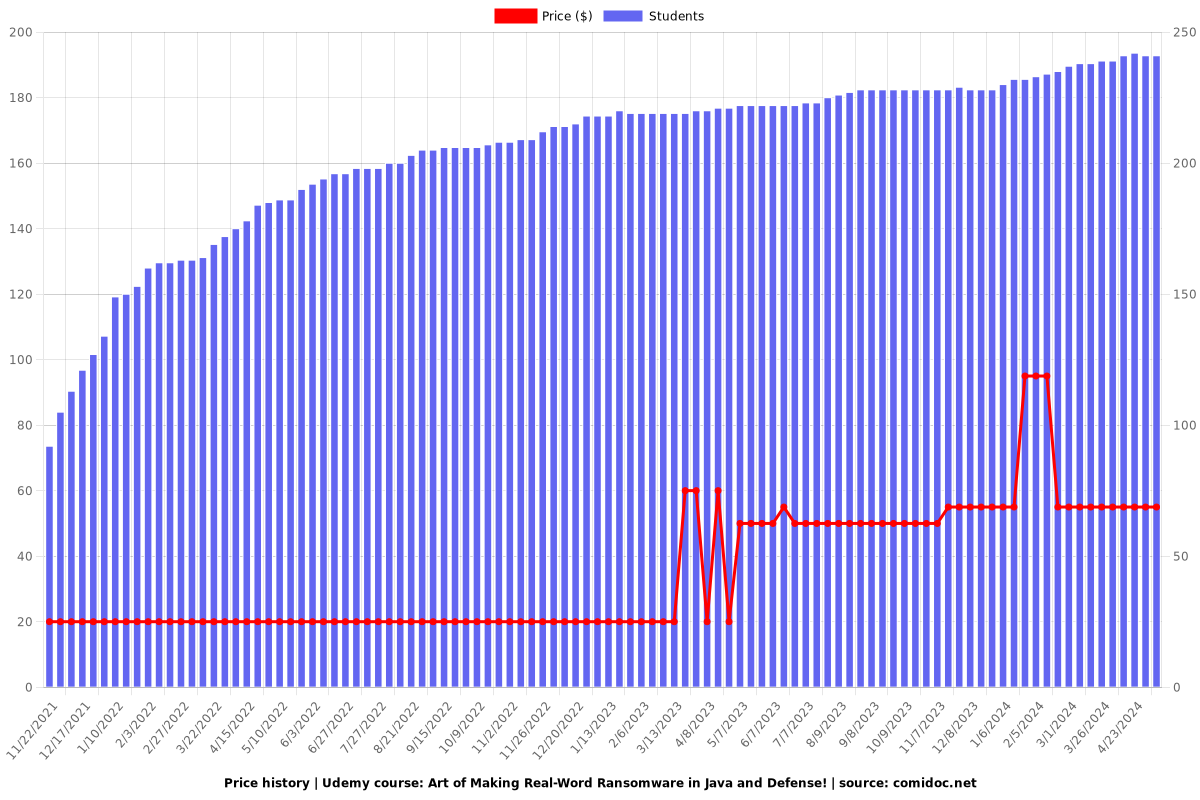
Price
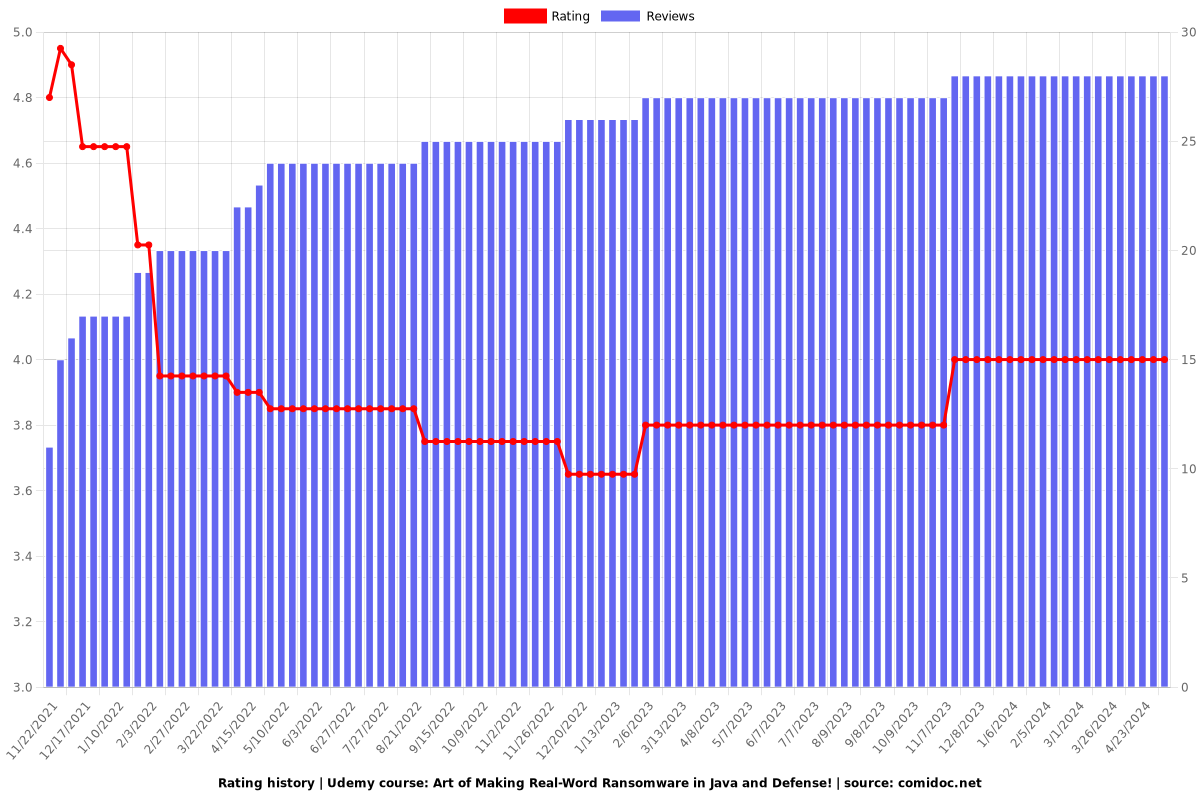
Rating
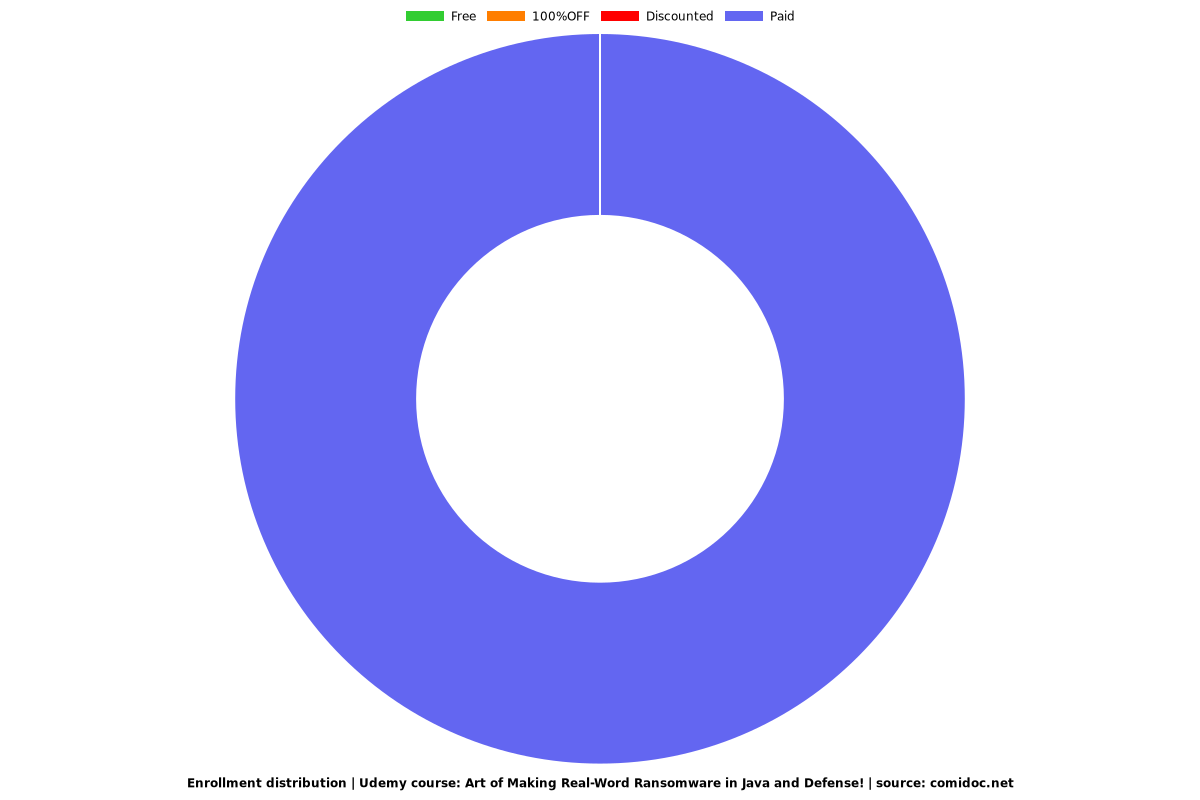
Enrollment distribution