सीखें Ethical Hacking With Python 3 हिंदी में 2022.
Learn How to Do Ethical Hacking, Network Testing, penetration Testing

What you will learn
Create a Python Mac-changer Tool
Network Hacking
Crack WPA2
You will learn Number Of attacks to Crack WPA-WPA2
Gather Information About The Router Without Knowing The Router Password
Hack Wifi With GPU
Evil Twin Attack
More Videos such as Creating Backdoor Will Be uploaded On January 15 Video are in Development Mode
Capturing Login Information In Fly
Downgrade HTTPS to HTTP
MITM Attack With Ettercap
MITM Attack With Bettercap
Intercepting Connection
Downgrade HTTPS website To HTTP
Sniff Login Details Of HTTPS Website
DNS Spoofing
Hook Beef Code With Ethercap In The Air
Open Port Exploit - Network Attacks
Nmap Advance
Create A Deauthentication Attack With Python 3
Create A Network Scanner With Python 3
Create A Port Scanner With Python 3
Create A Network Sniffer With Python3
Capture Login Information In The Air With Python3 Coding
Understand Encryption
Why take this course?
Learn Ethical Hacking From Scratch With Python हिंदी में.
UPDATE :- CLIENT SIDE ATTACK WHICH INCLUDE CREATING UNDECTABLE BACKDOOR AND MANY OTHER STUFF WILL BE UPLOADED ON Aug 15 TO Sept 30 BETWEEN .
Why we need a wireless adapter :-
In virtual machine, network is shown as cable connected network and it cannot go to monitor mode. So for both of the above causes, we need external wireless adapter to run in monitor mode.
Oracle VM VirtualBox is a type-2 hypervisor for x86 virtualization developed by Oracle Corporation. VirtualBox was originally created by Innotek GmbH, which was acquired by Sun Microsystems in 2008, which was in turn acquired by Oracle in 2010.
Kali Linux is an open-source, Debian-based Linux distribution geared towards various information security tasks, such as Penetration Testing, Security Research, Computer Forensics and Reverse Engineering.
Python programming language good for hackers?
Python is used among hacking professionals for its powerful and user-friendly libraries. It provides readability and simplicity, which can help you complete your tasks more quickly and easily. Python libraries are also used for code-cracking, decoding, network scanning, and even network attacks.
For the best experience Student should Do more research what have been taught .
Kali Linux requires: -> Virtual Box
A minimum of 4GB RAM
Wireless Adapter For Wifi Hacking Section
Reviews
Charts
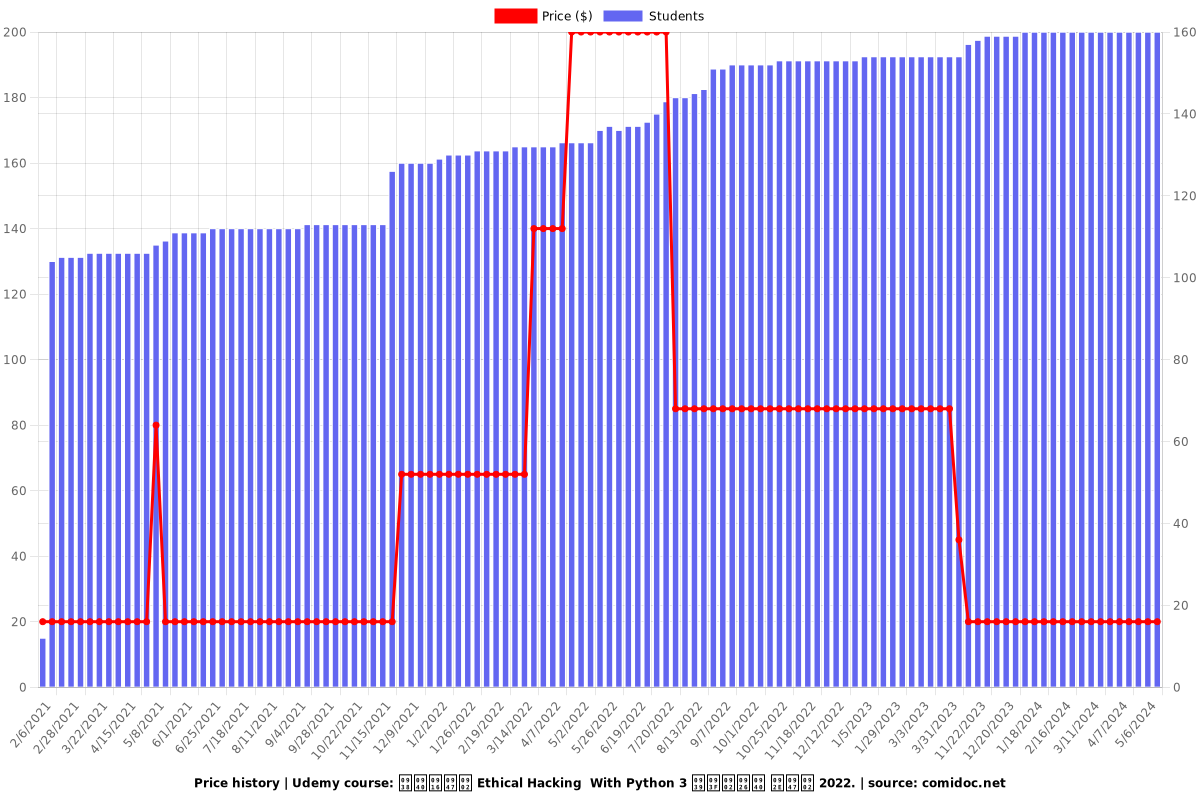
Price
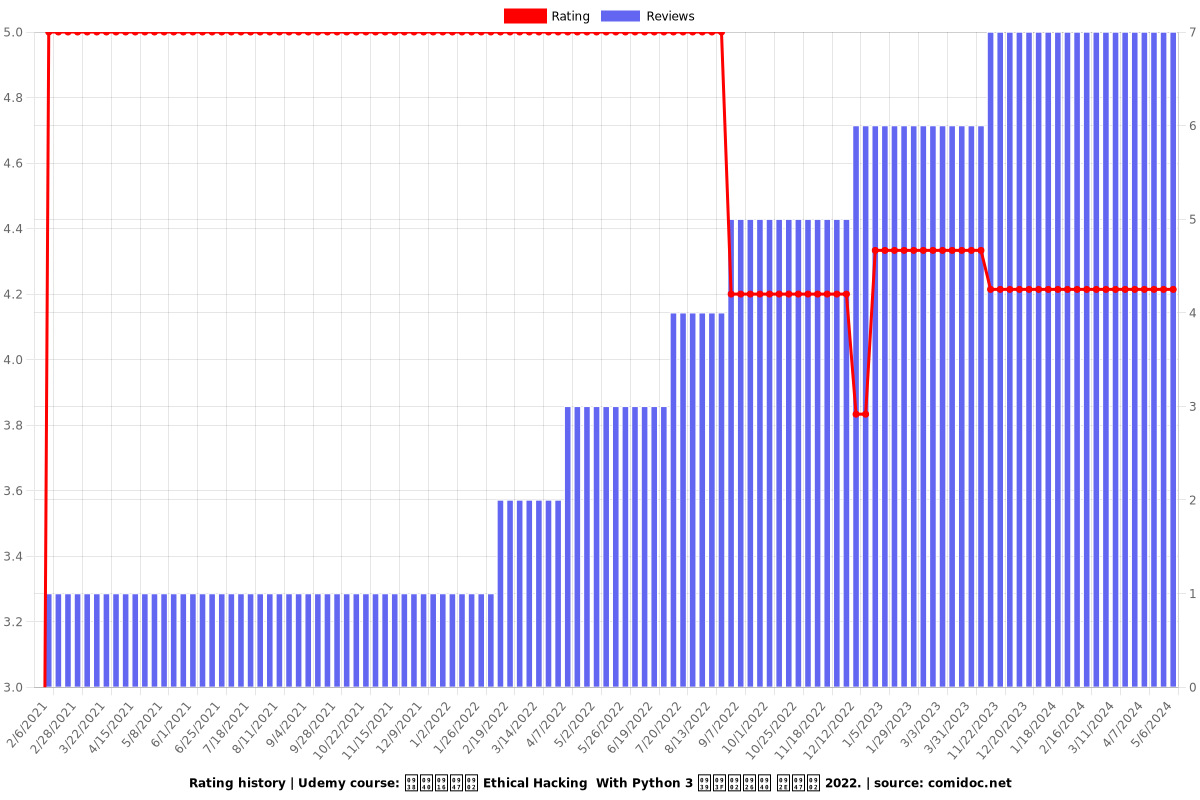
Rating
Enrollment distribution