Wireshark: Packet Analysis and Ethical Hacking: Core Skills
From basic to advanced network analysis using Wireshark! Ethical Hacking using Kali Linux: Passwords, Security, Protocol
4.68 (8364 reviews)

240,490
students
14.5 hours
content
Jan 2023
last update
$84.99
regular price
What you will learn
Learn how to troubleshoot networks using Wireshark.
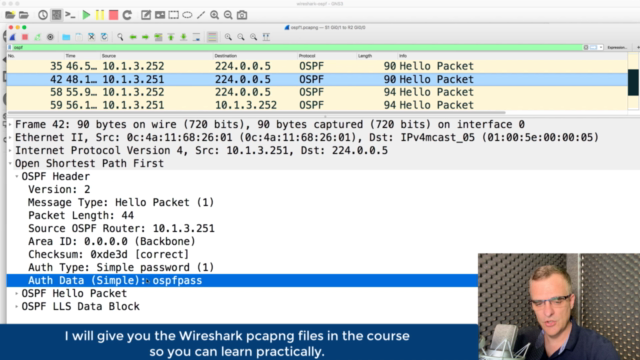
Capture VoIP, OSPF, HTTP, Telnet and many other protocols using Wireshark.
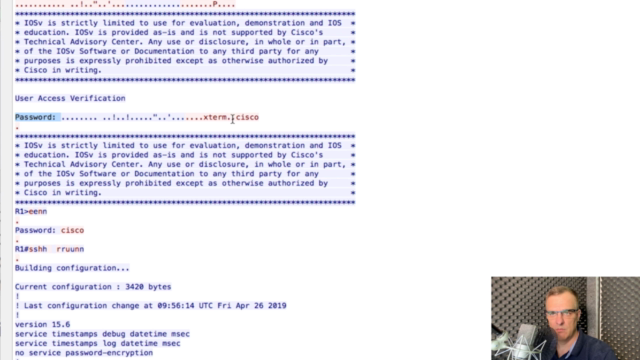
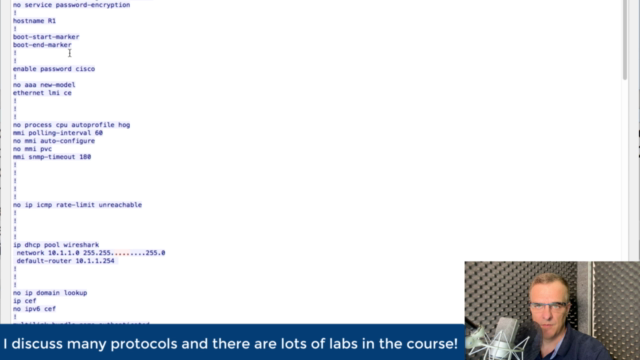
Learn how to use Wireshark for Ethical hacking.
Improve your job prospects by adding Wireshark to your resume.
Understand and interpret network protocols.
Hack Network Protocols using Kali Linux
Screenshots
Related Topics
2351336
udemy ID
5/3/2019
course created date
8/19/2019
course indexed date
Bot
course submited by