Remote Access Tool 2 (RAT2) : Desktop Capture and Keyloggers
Learn how to add keylogger, remote desktop capture and advanced remote command executions to RATs
4.39 (41 reviews)

979
students
6.5 hours
content
Dec 2024
last update
$69.99
regular price
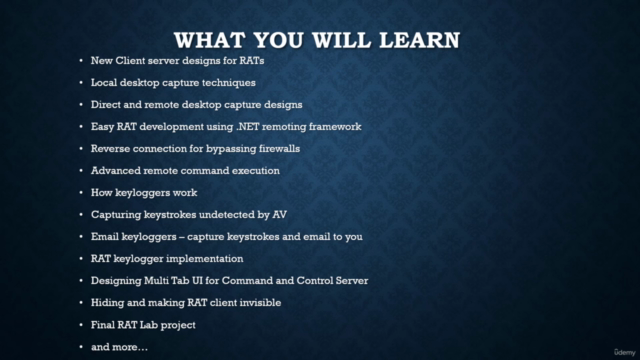
What you will learn
Client server designs for RATs
Local desktop capture techniques
Direct desktop capture via the network
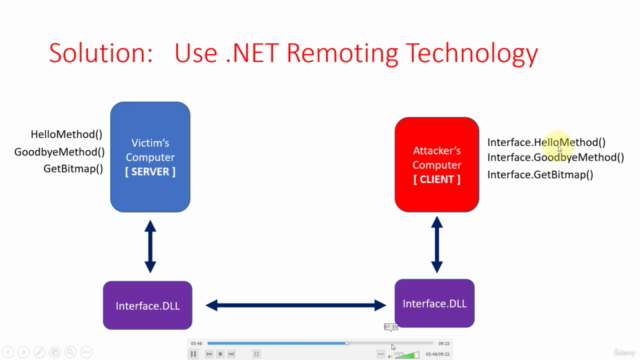
Using .NET remoting framework for RATs
Reverse connection techniques for bypassing firewalls
Advanced remote command execution
How keyloggers work
How to capture keystrokes that is undetectable by windows defender
Testing RATs using virtual machines
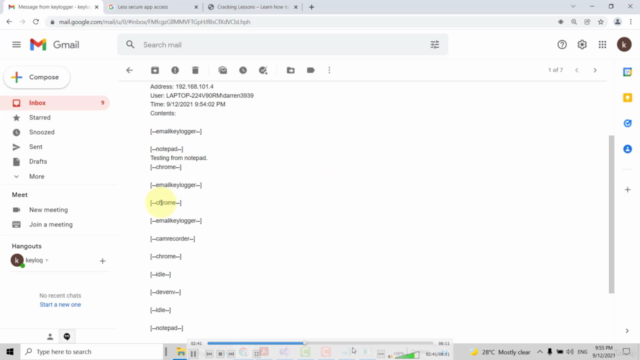
Automatically emailing captured keystrokes
RAT keyloggers
RAT Lab Projects
and more...
Screenshots
4403229
udemy ID
11/18/2021
course created date
12/25/2021
course indexed date
Bot
course submited by