Palo Alto Networks Firewall - Hands-On Cyber Security Course
Learn about Cyber Security Attacks and How to Defeat them with Palo Alto Networks Firewalls
4.65 (91 reviews)

1,672
students
2 hours
content
Jun 2021
last update
$44.99
regular price
What you will learn
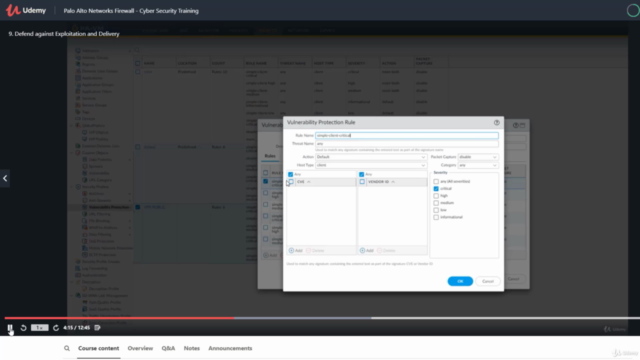
Learn about the Palo Alto Networks firewall security features such as Wildfire , Vulnerability Protection and DNS Security
Understand the methodology and motivations of cybercriminals and attackers.
Understand when, where, and how to use your Palo Alto Networks firewall to protect your network.
Learn how to optimize your Palo Alto Networks Firewall setup and avoid misconfigurations that could lead to a breach.
Screenshots


3995094
udemy ID
4/20/2021
course created date
6/14/2021
course indexed date
Bot
course submited by