Reverse Engineering & Malware Analysis of .NET & Java
A Beginner's Course on Reverse Engineering and Analyzing Malicious .NET and Java Executable Files
4.67 (91 reviews)
12,919
students
3 hours
content
Dec 2024
last update
$54.99
regular price
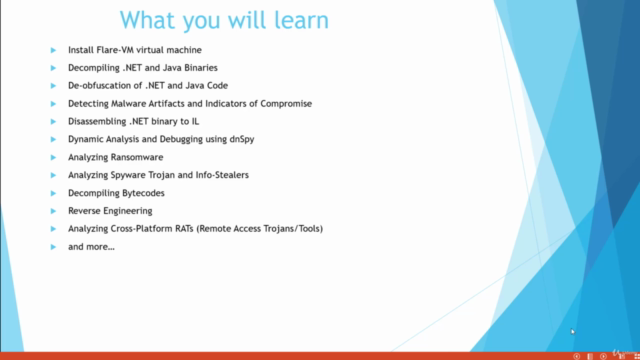
What you will learn
Decompiling .NET and Java Binaries
De-obfuscation of .NET and Java Code
Analyzing .NET and Java Malware
Detecting Malware Artifacts and Indicators of Compromise
Using Flare-VM Malware Analysis Tools
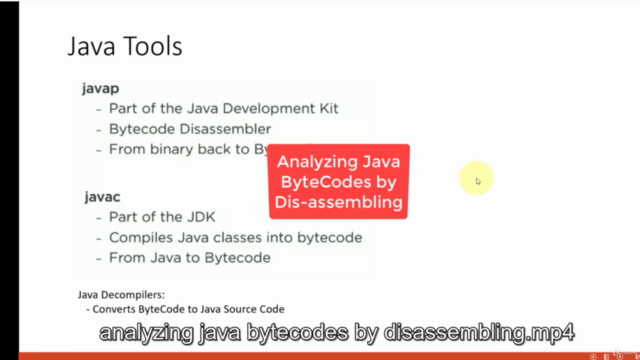
Disassembling .NET binary to IL language
Decompiling .NET binary to C# or VBNET
Static Analysis of .NET and Java Executable
Dynamic Analysis and Debugging using dnSpy
Setting up Malware Analysis Lab
Analyzing Ransomware
Analyzing Spyware Trojans and Info-Stealers
Identifying Native Files vs .NET and Java Files
Decompiling Java Bytecode to Java Source
Reverse Engineering
Analyzing Cross Platform RATs
and more...
Screenshots
Related Topics
4073476
udemy ID
5/24/2021
course created date
6/7/2021
course indexed date
MesterPerfect
course submited by