Reverse Engineering & Malware Analysis - Intermediate Level
An Intermediate Level Course on Reverse Engineering and Analyzing Malware
4.49 (305 reviews)
12,387
students
5.5 hours
content
Dec 2024
last update
$74.99
regular price
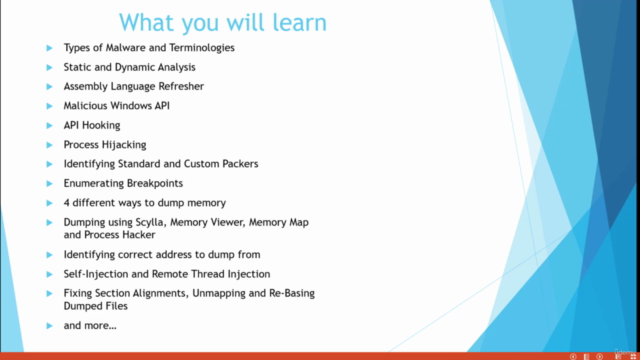
What you will learn
Types of Malware and Terminologies
Static Analysis
Dynamic Analysis
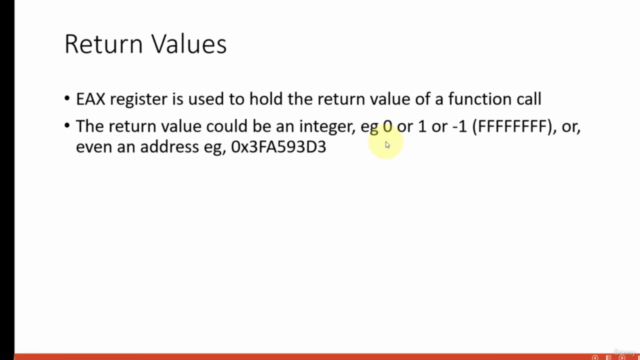
Assembly Language Refresher and Malicious APIs
API Hooking, Process Hijacking, Dumping Memory
Identifying Standard and Custom Packers
Unpacking Packed Malware
Enumerating Breakpoints and Memory Tracing
Hooking VirtualProtect, VirtualAlloc, GetProcAddress, CreateProcessInternalW and other common API's
Using Scylla Plugin to Dump Memory, Fixing IAT Tables
Using Delphi Interactive Reconstructor
Dumping Memory from Memory Viewer, Process Hacker and Memory Maps
API Enumeration Count Trick To Know When to Dump
Self-Injection and Remote Thread Injection
Fixing Section Alignments, Unmapping and Re-Basing Dumped Files
and more...
Screenshots
Related Topics
4108556
udemy ID
6/8/2021
course created date
7/22/2021
course indexed date
Bot
course submited by