Learn Python & Ethical Hacking From Scratch
Write 20+ hacking programs to learn hacking and programming at the same time | No prior knowledge required
4.65 (20469 reviews)
129,348
students
25 hours
content
May 2024
last update
$27.99
regular price
What you will learn
180+ videos (25 hours) on Python programming & ethical hacking
Write over 20 hacking and security programs
Learn 2 topics at the same time - Python programming & Ethical Hacking
No programming, hacking or Linux knowledge required
Write programs in Python 2 and 3
Write cross platform programs that work on Windows, Apple Mac OS & Linux
Have a deep understanding on how computer systems work
Install hacking lab & needed software (on Windows, Apple Mac OS and Linux)
Start from 0 up to a high-intermediate level
Learn by example, by writing exciting programs
Model problems, design solutions & implement them using Python
Have a strong base & use the skills learned to write any program even if its not related to hacking
Understand what is Hacking, what is Programming, and why are they related
Design a testing lab to practice hacking & programming safely
Interact & use the Linux terminal
Understand what MAC address is & how to change it
Write a python program to change MAC address
Use Python modules and libraries
Understand Object Oriented Programming
Write object oriented programs
Model & design extendable programs
Write a program to discover devices connected to the same network
Read, analyse & manipulate network packets
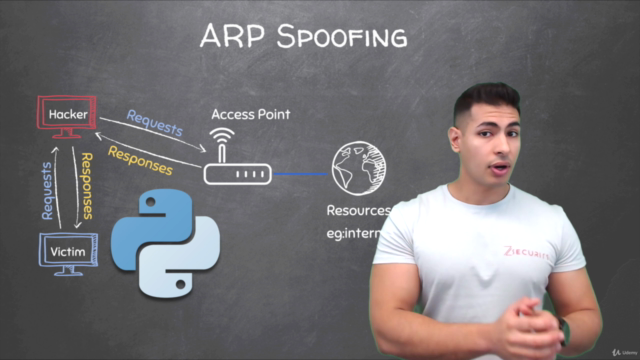
Understand & interact with different network layers such as ARP, DNS, HTTP ....etc
Write a program to redirect the flow of packets in a network (ARP spoofer)
Write a packet sniffer to filter interesting data such as usernames and passwords
Write a program to redirect DNS requests (DNS Spoofer)
Intercept and modify network packets on the fly
Write a program to replace downloads requested by any computer on the network
Analyse & modify HTTP requests and responses
Inject code in HTML pages loaded by computers on the same network
Downgrade HTTPS to HTTP
Write a program to detect ARP Spoofing attacks
Write payloads to download a file, execute command, download & execute, download execute & report .....etc
Use sockets to send data over TCP
Send data reliably over TCP
Write client-server programs
Write a backdoor that works on Windows, Apple Mac OS and Linux
Implement features in the backdoor such as file system access, upload and download files and persistence
Write a remote keylogger that can register all keystrikes and send them by Email
Interact with files using python (read, write & modify)
Convert python programs to binary executables that work on Windows, OS X and Linux
Convert malware to torjans that work and function like other file types like an image or a PDF
Bypass Anti-Virus Programs
Understand how websites work, the technologies used and how to test them for weaknesses
Send requests towebsites and analyse responses
Write a program that can discover hidden paths in websites
Write a program that can map websites and discover all links, subdomains, files and directories
Extract and submit forms using python
Run dictionary attacks and guess login information on login pages
Analyse HTML using Python
Interact with websites using Python
Write a program that can discover vulnerabilities in websites
Screenshots


Related Topics
1527300
udemy ID
1/26/2018
course created date
5/16/2019
course indexed date
Bot
course submited by