CrowdStrike: Zero to Falcon Admin
Disclaimer: This course offered independently by Blue Team Consulting, LLC and is not affiliated with CrowdStrike, Inc.
4.49 (2125 reviews)

9,460
students
4 hours
content
Mar 2025
last update
$44.99
regular price
What you will learn
Gain mastery of the Falcon platform: Learn how to navigate and use the various features of the CrowdStrike Falcon platform related to administrative duties.
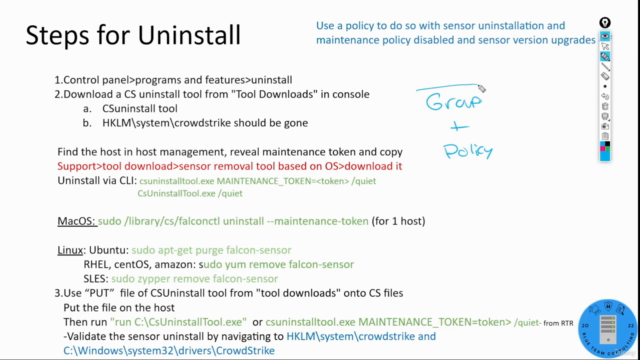
Learn the core principles of endpoint protection, including deployment, host management, troubleshooting, and response.
Learn best practices for security operations: Gain an understanding of industry-standard security practices and how to apply them to your organization.
Cybersecurity Engineering Concepts for Configuring an EDR Console
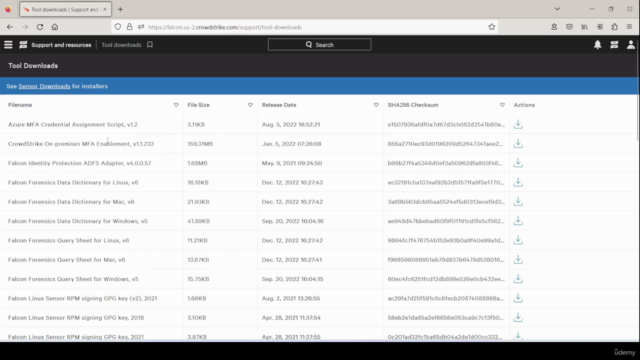
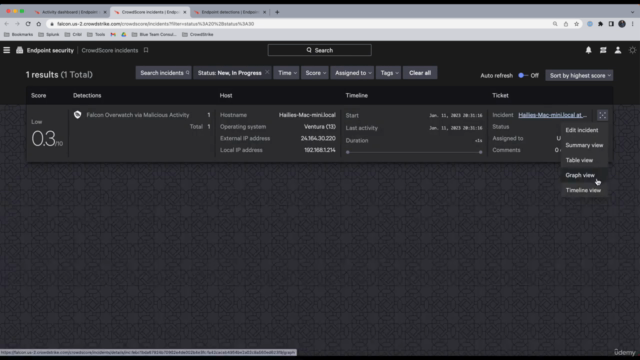
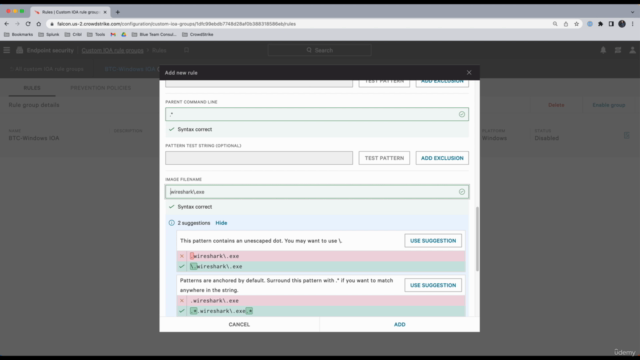
Screenshots
Related Topics
5167620
udemy ID
2/19/2023
course created date
4/5/2023
course indexed date
Bot
course submited by