Complete WIFI Hacking Course With Powerful MITM Techniques
Crack WPA/WPA2 PSK Passwords, MITM, Social Engineering , Aircrack-ng Suite, Advanced Password Recovery with Hashcat
4.46 (261 reviews)

20,095
students
2 hours
content
Mar 2023
last update
$64.99
regular price
What you will learn
Setting up wireless penetration testing lab
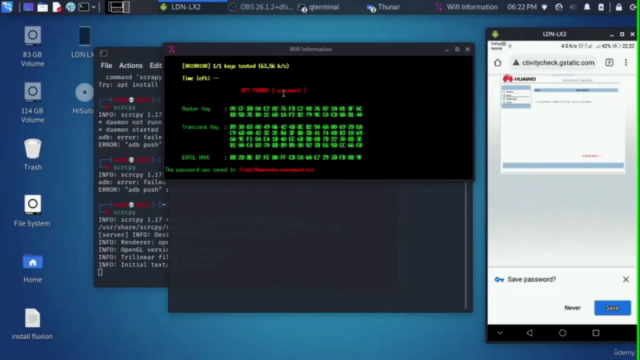
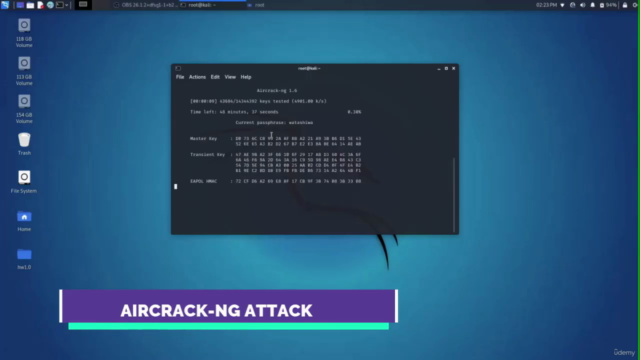
Crack WPA/WPA2 PSK passwords
Aircrack-ng suite (Airmon-ng, Airodump-ng, Aireplay-ng, Airbase-ng)
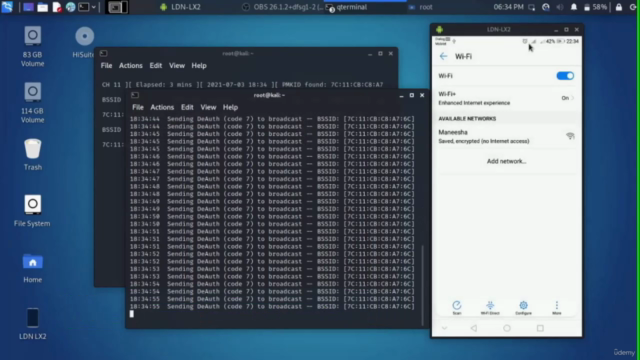
Denial of Service attack (DoS)
Hashcat (Brute-force attack, Dictionary attack, Combinator attack, Rule-based attack )
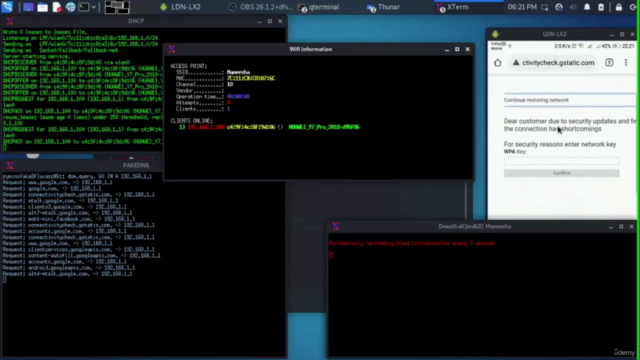
2 powerful MITM techniques
Evil twin attack using captive portral
Fake firmware upgrade method
Rainbow table attack with genpmk and cowpatty
Using CMD to view saved passwords
Creating simple batch script to steal saved passwords
Compiling batch script into undetectable and invisible EXE
Using a USB an simple social engineering to steal wifi passwords
WEP Cracking
Creating Evil-Twin AP from Scratch
Configuring SSL with Openssl
Dnsmasq and Hostapd
Integrating custom template into Airgeddon
Screenshots
Related Topics
4168526
udemy ID
7/6/2021
course created date
7/19/2021
course indexed date
Bot
course submited by