Complete Ethical Hacking Bootcamp
Learn Ethical Hacking + Penetration Testing! Use real techniques by black hat hackers then learn to defend against them!
4.63 (17984 reviews)

104,775
students
29 hours
content
Feb 2025
last update
$124.99
regular price
What you will learn
Learn Ethical Hacking from scratch & All 5 phases of Penetration Testing
Learn Python from scratch so you are able to write your own tools for ethical hacking
Setting up your Hacking Lab: Kali Linux and Virtual Machines (Works with Windows/Mac/Linux)
Create additional virtual *vulnerable* machines that we can practice our attacks on
Create trojans, viruses, keyloggers for ethical hacking
Learn how to bypass Firewalls & Intrusion Detection System with Advanced Scanning
Learn how to crack Wireless Access Point passwords
Bug Bounty: Discover all types of Web Application Bugs that could cause a threat
Learn how to gain access to any type of machine: Windows/Linux/MacOS
Sniff passwords over the local area network with Man In The Middle Attacks
SQL Injection, XSS, Command Injection and other techniques
Learn how to trick people into opening your program (i.e Social Engineering)
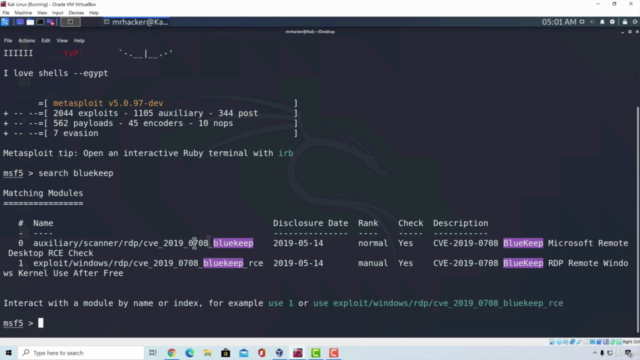
Learn Advance Metasploit Framework usage
Learn Basics of Linux and Linux Terminal
Master Information Gathering and Footprinting
Learn how to perform Vulnerability Analysis
Perform advanced scanning of an entire network
Perform Deauthentication Attack to disconnect everyone from the Wireless Access Point
Learn Website Application Penetration Testing from scratch
Learn Advance Nmap Usage
Code your own Advanced Backdoor that you can use in your Penetration Tests
Create Persistence on target machines
Perform newest Windows 7 + 10 exploits & attacks
Learn how to gain access to a router in various ways
Learn Networking & different Networking Protocols
Combine programming knowledge and ethical hacking knowledge so you can mix techniques and adapt them to different situations
Screenshots



3291970
udemy ID
7/2/2020
course created date
11/6/2020
course indexed date
Bot
course submited by