Advanced Ethical Hacking: Network & Web PenTesting-Part II_a
By JRDcademy: Become an Advanced in CyberSecurity, Network & Web application Penetration Tests (Hands-on Labs)

What you will learn
Way to get our service and products (Tools & Gift related to the course: FREE software & hardware) at our Facebook .com/JRDcademy page to excel in this course.
Working with BURPSUITE PROFESSIONAL instead of the COMMUNITY version (ranking between the 3 first best tools for PenTesting)
Labs Preparation (VirtualBox & Kali Linux installation & configuration), step-by-step guide & options to avoid provided ONLY by us & on Facebook/JRDacademy page
METASPLOIT, ARMITAGE (High-level Penetration Testing Software, find security issues, verify vulnerability mitigations & much more)
Fix Armitage Error, and Enjoy the Metasploit User Interface
Enumeration, Remote and Exploitation
Structured Query Language (SQL Injection)
Cross-site Scripting (XSS attack)
Vulnerability Scanning
Network Scanning, Nmap Scanning, Nikto, Dirb, Ettercap
Reverse Shells
Buffer Overflows, DoS Attack
Man-In-The-Middle (MITM) Attack
Privilege Escalation
Network Hacking
Wireless Hacking
Take Control Of Any Wi-Fi Network ESSID whether it is well-passworded or not
WEP/WPA/WPA2 Hole/pitfall
Interrupt the Connection of a Client's ip-address whether using WEP/WPA/WPA2 Protocols
Get the Handshake of WPA/WPA2 Protocols of a Wi-Fi ESSID
Crack Wireless WEP/WPA/WPA2 ESSID
Eavesdrop the Communication & The Reason Behind The Scene
Stealth Idle Scan
Bypass Antivirus in Windows Machine
Bypass Any Windows Login Password & Get Access To The System Administrator
Bypass Ubuntu Login Password & Get Access To The System Administrator
Bypass MacOs Login Password & Get Access To The System Administrator
Strengthen The Login Account Security Of Your Computer thrice Before Getting Access To The Admin's Screen
Essentials of CEH v10 in real-life (CEH - Certified Ethical Hacker)
Information Security
ElGamal, RSA, Diffie-Hellman (Encryption and Decription steps)
Router Hacking
Mobile Phones Hacking
Description
This course is all about Ethical Hacking and Security, which needs some Professional tools to proceed with, such as burpsuite_Pro for example.
This course covers syllabus of CEH v10 Certified Ethical Hacker version 10, mainly the Network activities, and some frequent web application vulnerabilities. Course has been designed in a way so that any novice, (from Zero level) to the advanced level of people in cyber security field can easily understand and can be well-benefited. As it is a step-by-step process, from zero to high level, we encourage you to try to understand exclusively the part one; then after, jump into the next parts to get what you need to know about cryptology, network establishment, firewall, hacking, eavesdrop, empower the security, etc...(as if you were sitting in a Master & PhD cryptology classroom).
Therefore, after completing our courses (parts 1 - 4), you will meet with the most used encryption techniques, methods used to mitigate the probability of being hacked by Black-Hat hackers.
-The most recent ways of hacking into a wireless network, no matter what protocols the Wifi was set with by its administrator. Furthermore, no matter how strong the Wifi password is, so that we dupe someone's network. We explain the reasons behind the scene of such attacks. Exploitation of the existed holes that the most used Operating Systems contain, such as (Linux based, Windows, Mac OS, Android)
We deeply explain why RSA is that so strong and why it is highly used in real-life cybersecurity, as well as AES encryption.
Most Well-known Encrypting Algorithms, such as ElGamal, RSA, Diffie-Hellman, and so on forth (Encryption and Decryption steps) are well described. It is crucial for cybersecurity engineers in Master and in PhD classes.
Note:
In this course, we supply to you not only videos for the practice, but also we provide a light text file for each part of the tutorial which is exclusively self-explanatory (a step-by-step process) so that we make it easier to learn according to the obligations that you might face while you want to continue with your practice.Example of a situation: you might need to continue with your tutorial where you are at a specific place, and don't want to disturb anybody while you forgot your earphone/headphone.
Content
Network Scanning, Network Establishment, Web Vulnerabilities Exploitation
Screenshots
Reviews
Coupons
| Submit by | Date | Coupon Code | Discount | Emitted/Used | Status |
|---|---|---|---|---|---|
| - | 5/31/2020 | C1D8D36JEANEE98D24B6 | 20% OFF | expired | |
| - | 2/7/2021 | JRD_ACADEMY_PART-2 | 0% OFF | expired |
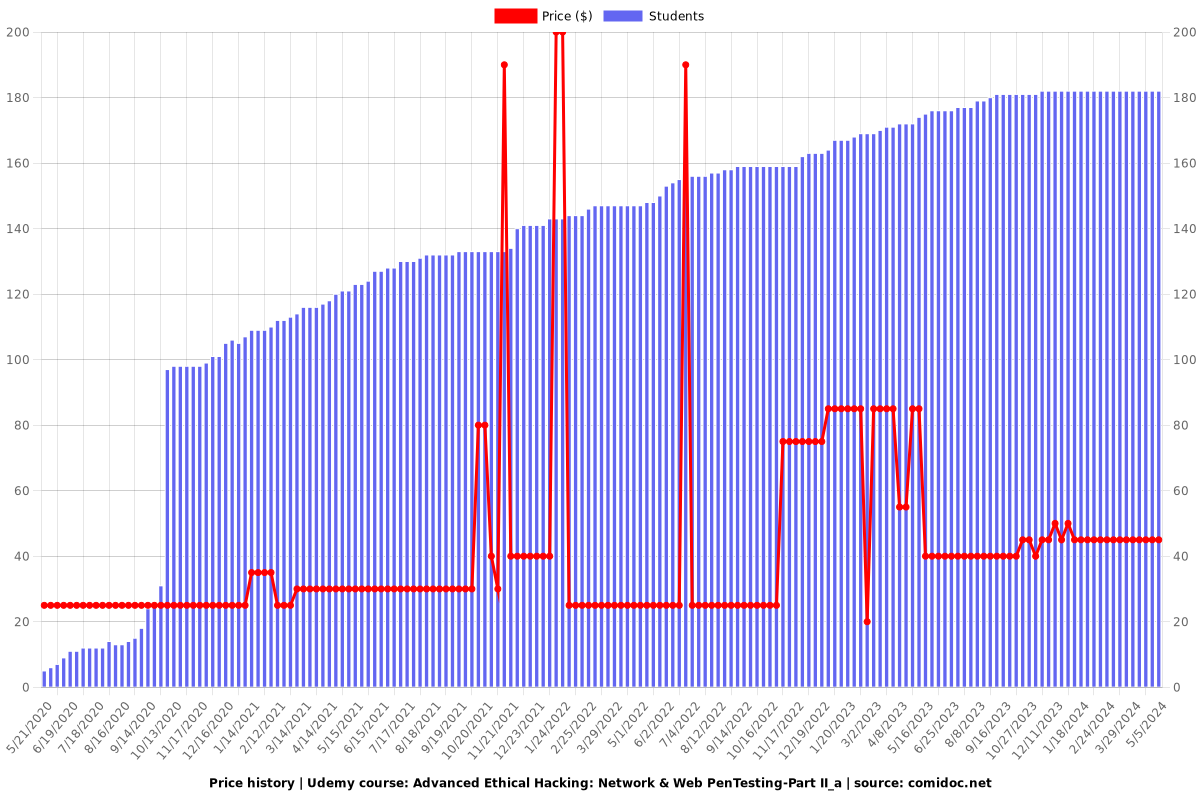
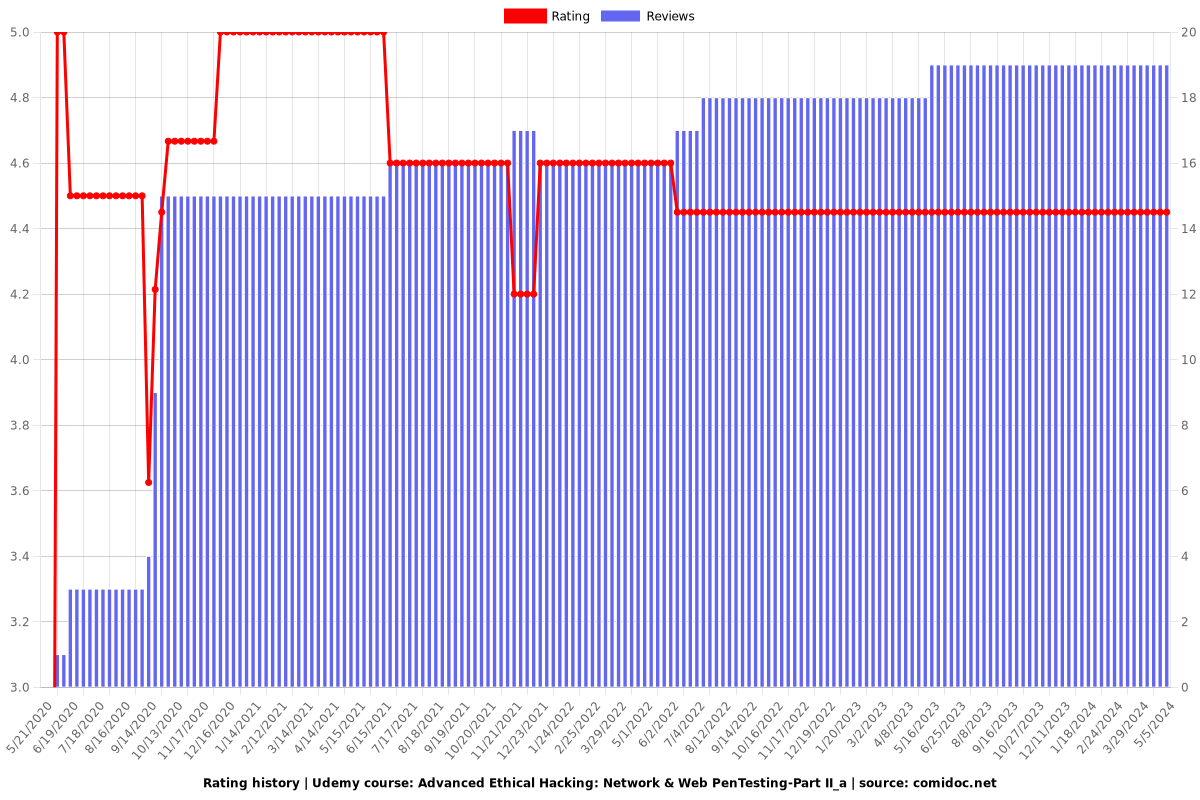
Charts
Price
Rating
Enrollment distribution